 Blog
Blog
Understand and Detect vCenter Vulnerability Exploitation
Jeff Costlow
September 23, 2021
VMware disclosed security flaws which have serious implications for any organization using vCenter. The most critical disclosure, CVE-2021-22005, is an arbitrary file upload vulnerability which allows an attacker to execute code on unpatched vCenter Server devices. Other vulnerabilities provide additional avenues for remote code execution and privilege escalation. When strung together, these vulnerabilities could allow an attacker to inflict significant damage in a short period of time.
The VMware centralized management utility vCenter Server is widely used, upping the potential impact of an exploit—and it's attractiveness to bad actors. While network access is required to leverage the vulnerability, as VMware acknowledged, you should act under the assumption that someone is already on your network, looking for an avenue to perform remote code execution. These VMware security flaws allow that and then some.
CISA has warned that the vulnerability is being actively exploited, in addition to reports of scanning behavior seeking environments with vCenter. The first step to reduce your enterprise's exposure to these vulnerabilities is to heed VMware's advice to patch these devices as soon as possible. The second step is to closely monitor your network for any anomalous activity that may indicate that a device has already been compromised.
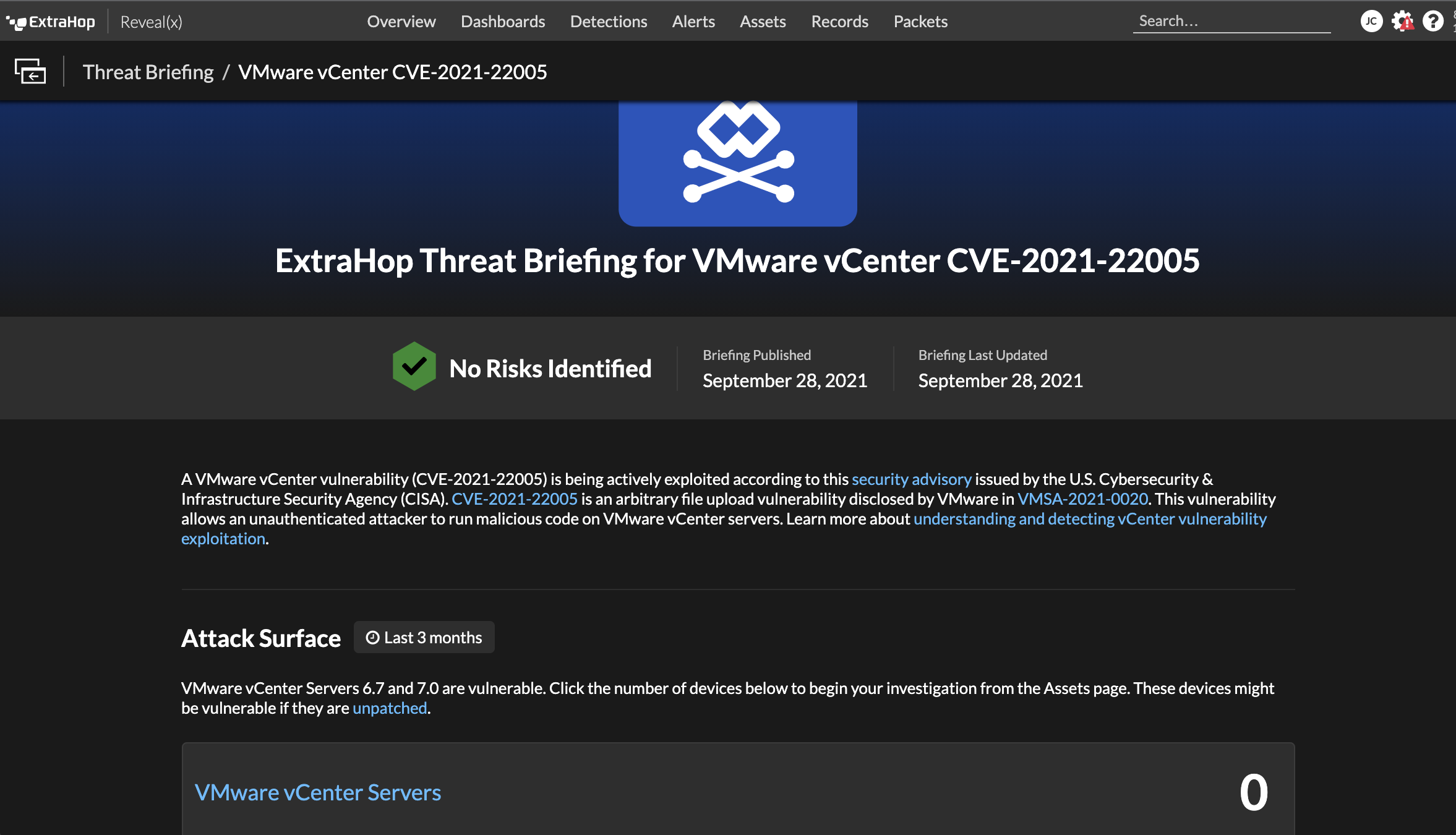
ExtraHop has added a threat briefing for CVE-2021-22005 and is in-progress adding a detection for the recently-posted exploit. Further, ExtraHop Reveal(x) discovers all VMWare vCenter Servers, giving a clear picture of whether an organization is affected by the vulnerability.
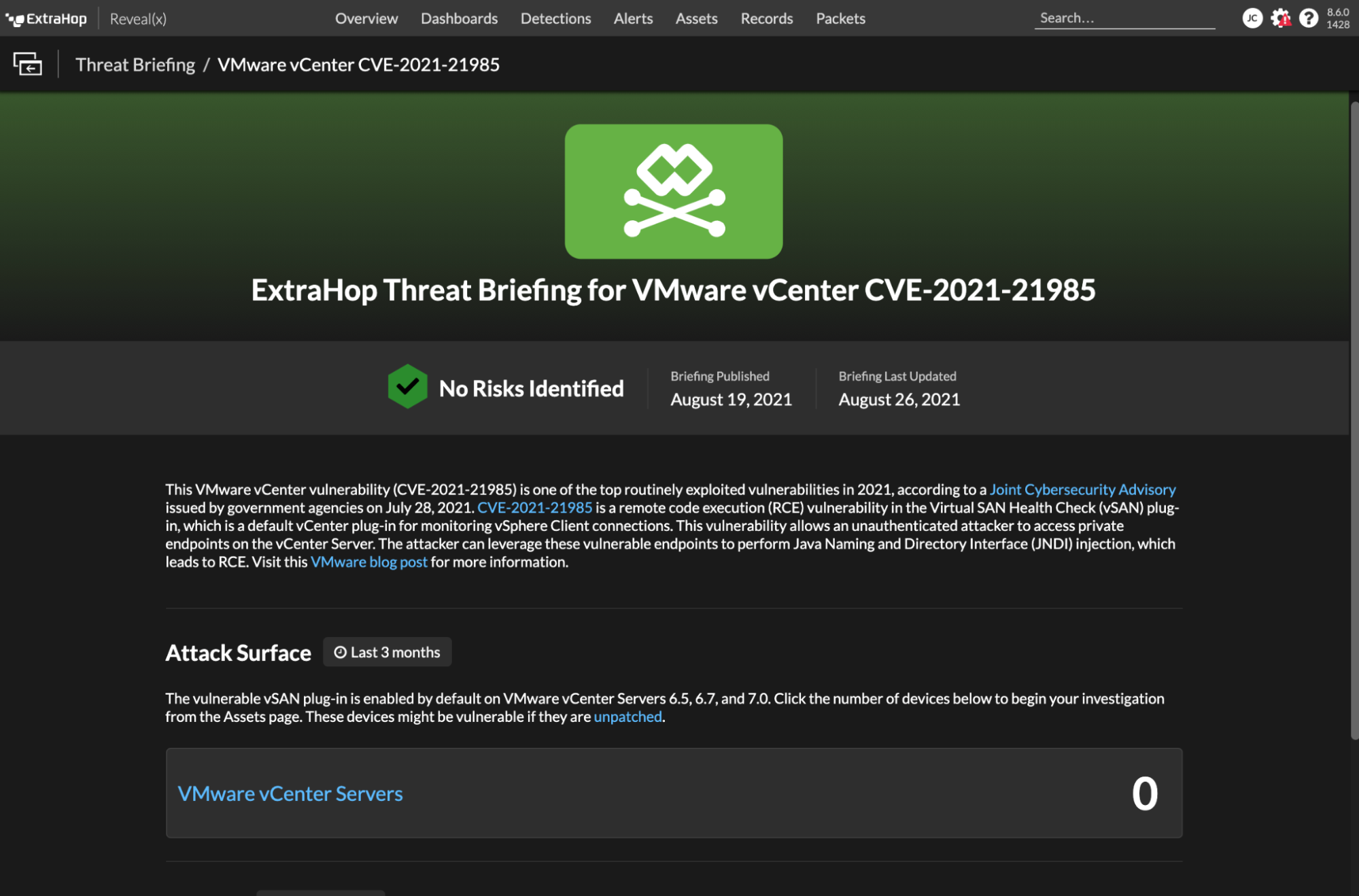
Previous vCenter Vulnerability
The Threat Briefing for the previous vCenter Vulnerability (CVE-2021-21985) released in Reveal(x) on August 19, 2021, is available to all customers and will show all vCenter servers in the customer environment.
Detect Attacks Exploiting the vCenter Vulnerability
While this vulnerability presents a novel means for an attacker to gain remote code execution capabilities, adjacent behaviors that may indicate a compromise are detectable using ExtraHop Reveal(x) 360—for example, the subsequent lateral movement necessary to reach valuable systems or data.
In addition to a PoC being quickly posted, there are widespread reports of scans seeking to identify vulnerable vCenter Servers.
CVE-2021-22005 scanning activity detected from 116.48.233.234 (🇭🇰).
Target:
VMware vCenter servers vulnerable to arbitrary file upload leading to remote code execution (https://t.co/JWfc7rHuUK).#threatintelpic.twitter.com/mDFQtyx8IG
— Bad Packets (@bad_packets) September 22, 2021
Detect Malicious Scans for vCenter
The vCenter Server vulnerability relies on an attacker having network access to port 443, which is the default port used by vCenter to listen for data from its clients. VMware's documentation instructs vCenter Server administrators to allow traffic through their firewalls at port 443 to enable vCenter functionality. Attackers may use port and network scanning to discover vCenter Server instances to exploit. Instances of such scanning from 116.48.233.234 have been reported.
ExtraHop Reveal(x) customers can discover whether their environment, and particularly their vCenter Server instances, have had any communication with IP addresses, such as that identified above, known to be scanning for vulnerable vCenter Server instances. If any external communication is found, then the server may be exposed to the internet. Customers may want to block internet access to the server.
Reveal(x) customers can also check their detections tab to see whether any unusual network or port scanning activity has been detected. Closely observing further network activity to and from vCenter Server instances can enable defenders to catch lateral movement that may follow successful exploitation of the vCenter Server vulnerabilities.
For a walk-through of how attackers move from network reconnaissance to active attack, enter our online demo.
Discover more